Go to https://haveibeenpwned.com/ to find out if your email or password has been involved in a data breach.
In this blog, we cover 3 important aspects of securing your data :
1. Safe Passwords: The Do's and Don'ts
2. Password Encryption
3. Two-factor authentication
We finish the blog by discussing how meeting the three criteria above only leads to frustration because you're constantly resetting passwords and taking ages just to sign into your email. However, safe passwords, encryption, and 2FA are essential to keeping your data safe. So, if you want to jump ahead, click here, to read Part III: 1PASSWORD to Manage Them.
If you missed Part I: The History of Passwords, you can read the blog now.
The Do's and Dont's of Passwords
Did you know that 81% of data breaches are due to poor password security?
(Verizon Data Breach Report, 2021)
Do use a variety of numbers, letters, and symbols.
Don't include common words like middle names, dog names, or even words found in the dictionary without changing the spelling. Example: If you want to include the word "french fry" in your password because you eat french fries every day for lunch. Use something like "Fr3nc1-1FrI instead.
Do change your password regularly
Don't repeat passwords
Do make your password long
Don't use numbers or alphabetical sequences (1234... ghjk...)
Do use password manager (read Part III: 1PASSWORD to Manage Them All)
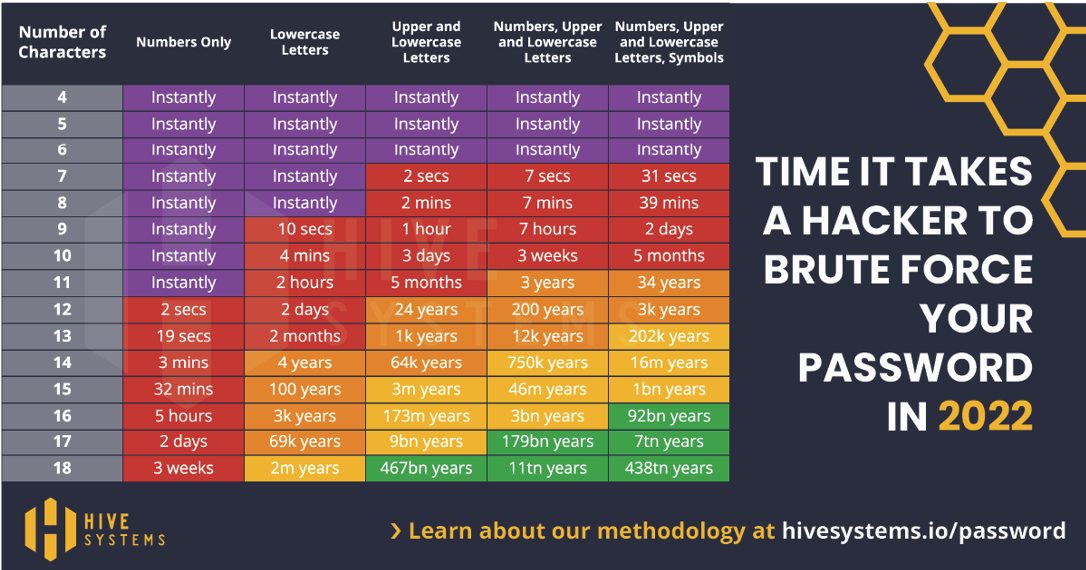
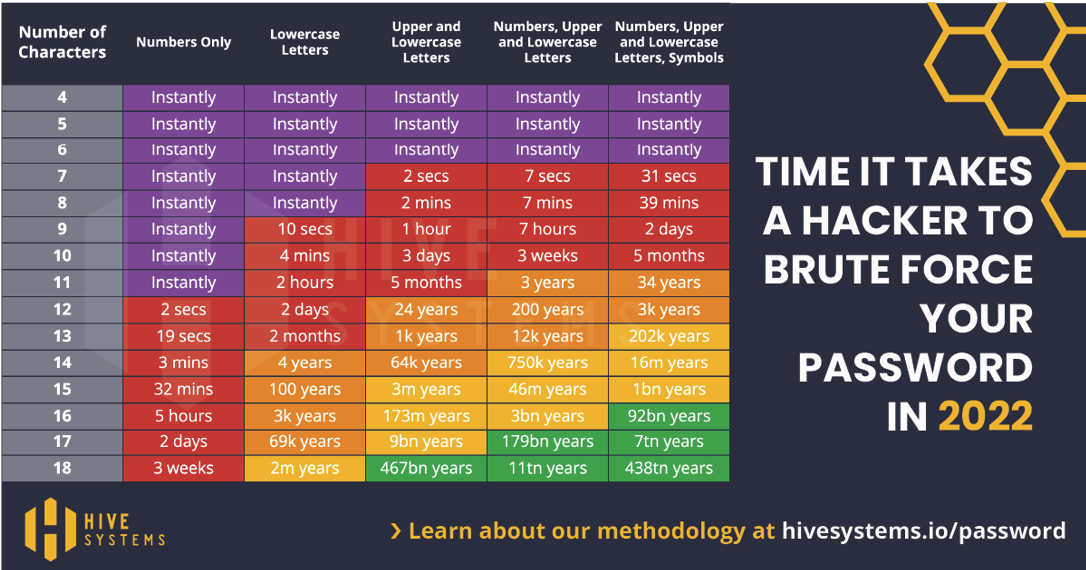
Below you can see how the stronger the password, the longer it would take a hacker to figure out your password.
However, safe passwords are not secure enough, so your passwords are likely encrypted.
What is Password Encryption?
A password is often the only line of defense between you and your personal information. As we discussed in Part 1: The History of Passwords, when an MIT professor created the first password system, it wasn't long before someone figured out how to hack the passwords.
Now, databases that store your password encrypt them. Essentially, encryption puts your password through a randomizer and scrambles the characters.
When learning about password encryption, there are four common types you will come across:
- Symmetric key:
- Everyone has a key. A password goes through the key and gets scrambled, then saved on a database. When you fill in a password, the scrambled code goes back through the key and is decrypted. A hacker would have to steal the key to figure out the decryption.
- Public key:
- Secure logging method that does not use passwords but instead SSH. SSH (or the lock symbol you can see to the left of your URL) is a secure way for two computers to connect remotely. This is how passwordless logins work.
- Hashed:
- First off, hashing is not considered encryption. Encryption is two-way, as we saw when reading about symmetric keys. Hashing uses an algorithm that transforms your password.
- This process comes before hashing. Random characters are added to the beginning and end of your password. Then that appended password goes through the hashing process.
Okay, okay. My password is safe; it is encrypted; why do I still need 2fa?
The sad truth is more than 1,000,000 passwords are stolen every week, according to the 2019 Breach Alarm. Yes. that is six zeroes, to make one million stolen passwords every week. As mentioned above, hackers are constantly improving their decryption methods. That's why 2FA(two-factor authentication) is so important. 2FA provides two lines of defense between a hacker and your personal information. The first is something you know, like a password, and the second is something you have, like your cellphone. The hacker is now required to have access not only to your decrypted password but to your second line of defense. Here at Pine Cove, we get asked many questions about 2FA because it can be a pain to implement, train employees, and keep using it. However, with proper implementation and settings, 2FA can make your information secure, reliable, and easy to access. If you want to learn more about 2FA, read our blog here.
Are Safe, Encrypted, and 2FA-Enabled Passwords Feasible? The Answer is No (But you already knew that)
How are you supposed to remember 50 different randomized passwords? How are you always supposed to remember your password and use 2FA in a timely fashion? Oh yeah.. let's be honest, you're not going to remember them, so you end up constantly hitting that "forget your password?" button. You're going to get frustrated when after you reset your password, you still have to type in a code that's sent to your cellphone, which leads to the following stat:
75% of Americans are frustrated with passwords.
(2019 Google survey)