What happened?
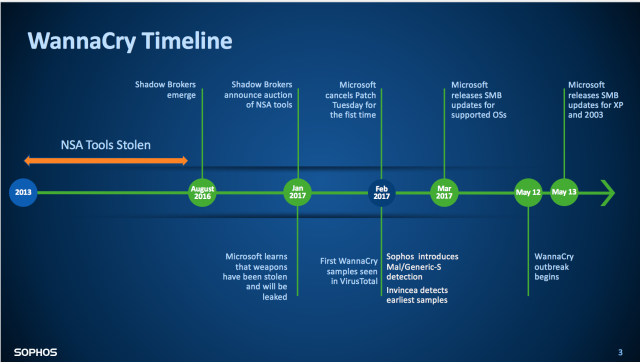
"The story of the WannaCry ransomware attack began sometime between 2013 and 2016, when the NSA’s exploit tools were stolen. In August 2016, Shadow Brokers revealed itself, and six months later announced the auctioning of NSA tools it had acquired.
Learning that the exploits targeted Windows SMB, Microsoft released a patch in March. When the outbreak hit two months later, it was clear that organizations and individuals had either neglected to apply the patch or were using outdated versions of Windows."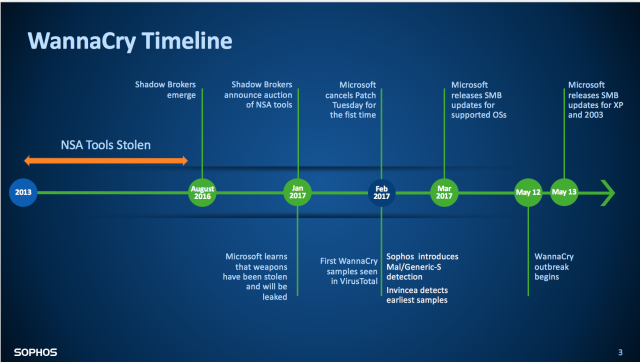
"The investigation revealed a three-stage attack, starting with remote code execution and the malware gaining advanced user privileges. From there, the payload was unpacked and executed. Once computers were hijacked, it encrypted documents and displayed ransom notes."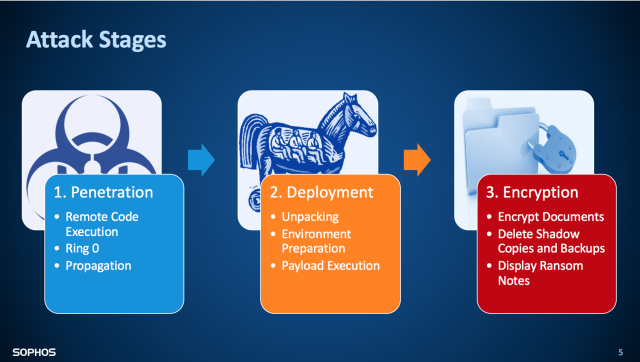
Lessons Learned from WannaCry:
"James Lyne, Sophos head of security research, offered this advice yesterday at InfoSec:
- Don’t get distracted by the “big, sexy talks” like government-sponsored attacks and nation-state cybercrime. They are interesting topics to be sure, but …
- Stay grounded in the opportunistic attacks that target businesses every day, like ransomware and the recent WannaCry outbreak.
- Focus on the security basics — the simple things like using endpoint security, staying on top of patching and using strong passwords.
That advice could have saved organizations from a lot of pain last month. Paying attention now could help them prepare a much stronger defense against attacks to come."
What can Pine Cove do to protect your business moving forward?
Pine Cove Consulting provides organizations with premier cyber-crime fighting protection through Sophos. Clients who work with Pine Cove to protect their organizations had no issues with this massive ransomware attack. In fact, we help our clients fend off thousands of ransomware attacks every single day. Many companies across the nation are now setting aside money to pay off hackers as part of their budget. We recommend that your organization instead invest in security which can prevent the loss of capital and precious personal data from the beginning. If this is a solution you would like to explore more we would recommend contacting us online.
Read more at: https://nakedsecurity.sophos.com/2017/06/07/infosec-2017-how-to-protect-yourself-against-the-next-wannacry/